THE BLOG
This post is the third in a series of posts on Route Redistribution. If you didn’t yet read the first two, here are the links:
So ...
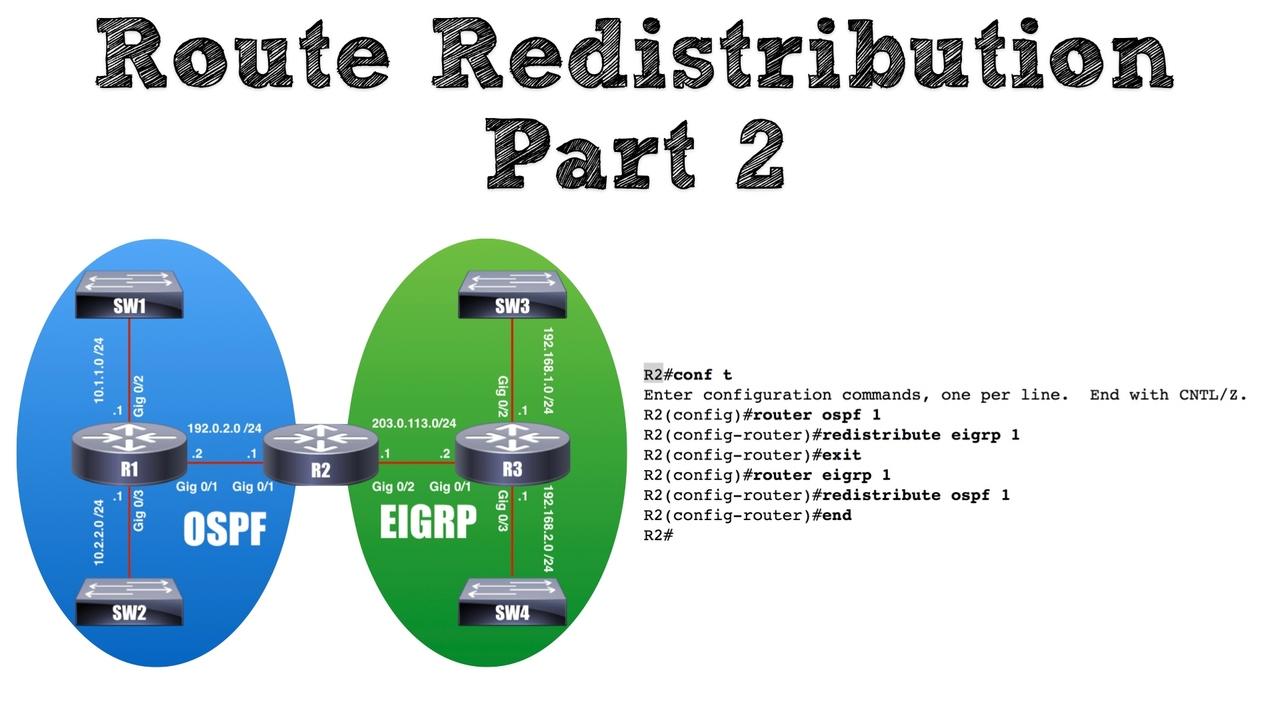
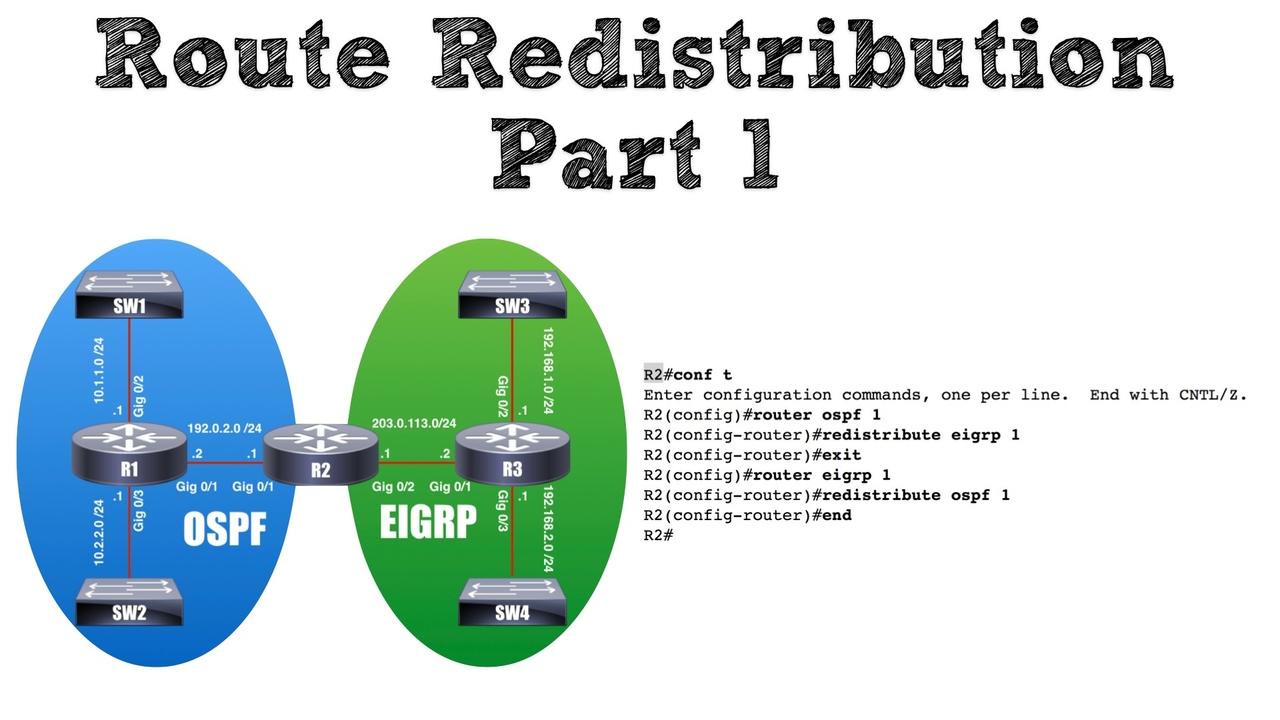
In a previous post, we considered the need for route redistribution, and we also took a look at some configuration examples. This posts builds on that previous configuration and discusses how we can f...
If the security track is on your radar, particularly CCNA Security, you need to have a working understanding of configuration and troubleshooting with Cisco's Adaptive Security Device Manager (ASDM).
...Our organizational IT environments are constantly changing, driven by factors such as telecommuting, cloud technologies, and BYOD (Bring Your Own Device) policies. This requires modular and dynamic ar...
Introduction to Route Redistribution
Until there is one routing protocol to rule them all, there is a need to have multiple routing protocols peacefully coexist on the same network. Perhaps Company ...
I get asked a lot about home lab equipment by those interested in studying cybersecurity, particularly CCNA Cyber Ops and CompTIA CySA+ students. In this new video, I'll give you a look at my setup, a...
Whenever someone asks me what direction they should focus their IT career, particularly in regard to cybersecurity, my answer is always the same: “It depends.” It’s usually not a very satisfying answe...
One question that I get asked all the time goes something like this: “How can I break into the cybersecurity field without any experience?” We hear the stats all the time about zero-percent cybersecur...
Last month I had the privilege of presenting a session at Cisco Live US 2018 (in Orlando, Florida). If you couldn't make it to the live event, you can now check out the video of my presentation by cli...
I recently returned from the Cisco Live US 2018 event in Orlando, Florida. It was a great experience, with lots of conversations, sessions, and insight. You can expect more content about what I learne...
I’m afraid we’ve over-romanticized the concept of cyber security in many ways. We imagine ourselves as Mr. Robot, staring at our terminals intensely, valiantly defending against state-sponsored DDOS a...
In this video, we'll take a look at The Onion Router, better known as the Tor browser. I'll demonstrate how Tor relays traffic through proxies to anonymize web traffic, and discuss some practical uses...
Today's networks face many security threats. The good news is, even without being security experts there are some best practices we can put into place to better protect our networks.
In the latest ep...
In this new video, you'll learn the need for wireless LAN (WLAN) security, along with multiple approaches and protocols for better securing your wireless LANs.
Topics include:
- War Driving
- MAC Fil ...
One of the hottest topics in IT is Cyber Security. It's estimated that by 2019 or 2020, there will be 6 million jobs in cyber security, with 25 percent of those jobs (i.e. 1.5 million jobs) vacant. Th...
In this post, I'm excited to share with you my latest podcast episode, where I'm interviewing my good friend and world-renowned Cisco trainer Anthony Sequeira.
In this episode, Anthony discusses:
-
...
I’m thrilled to announce this will be my second year speaking at Cisco Live US (CLUS), and it would be great if you could join me for my session. Last year, it was awesome getting to meet so many of m...
A national survey from Common Sense Media found that adults spend over nine hours each day in front of various screens – including computers, tablets, phones and televisions. I will confess that the f...
The Internet of Things
While shopping for an outdoor barbecue grill this past summer, the reality of the ever-increasing Internet of Things (IoT) really hit home with me. If you aren’t familiar wit...
Cisco recently introduced major updates for their CCIE Collaboration written and lab exams, jumping from version 1.0 of these exams directly to version 2.0. If you want all the details, you can ...
A little over three years ago, I left my full-time job with a Cisco Learning Partner (CLP) to venture out on my own and start Kevin Wallace Training, LLC. Since that time, the Cisco learning com...
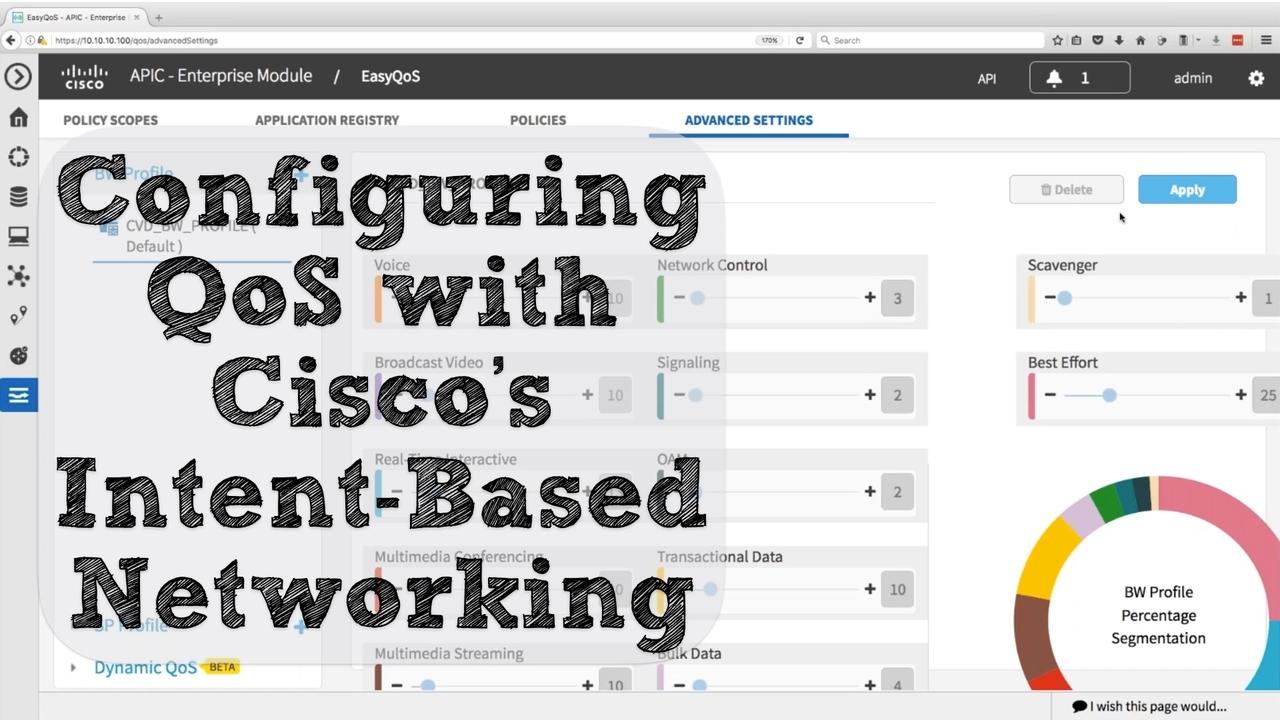
Over the past few months, you might have noticed Cisco’s publicity push regarding intent-based networking. The first time I saw this new brand messaging was at the Las Vegas McCarran Internation...
On any CCIE lab, time is your most precious commodity. Opinions vary about the best time saving strategies. Some people would have you spend the first 30 minutes of your lab carefully reading th...
Last week (on Cyber Monday), I did a webinar covering the theory and configuration of multiple QoS mechanisms. Here's what you'll learn in this replay of that webinar:
- Learn QoS Mechanisms
- U ...
I recently did a Facebook Live session covering 5 major Software Defined Networking (SDN) concepts. If you missed the live session, or just want to watch a replay, check out this video.
We cove...
I recently did a Facebook Live session covering the fundamentals of Cisco Collaboration technologies. If you missed it, or want to see it again, here's a replay.
Topics covered include:
- Trad ...
Let's say you have one or more IP routes that you don't want appearing in a router's IP routing table. The reason might be for security or for router performance, as a couple of examples. With O...
If you’re one of the 200,000+ Cisco customers using a Cisco Unified Communications Manager (CUCM) server to support your Cisco IP Phones and soft clients, this blog post is for you. Specifically, Cisc...
The Need to Know MQC in a World of Automation
These days, Quality of Service (QoS) can be configured relatively easy. If we’re using the APIC-EM as a network controller to manage our routers and swit...
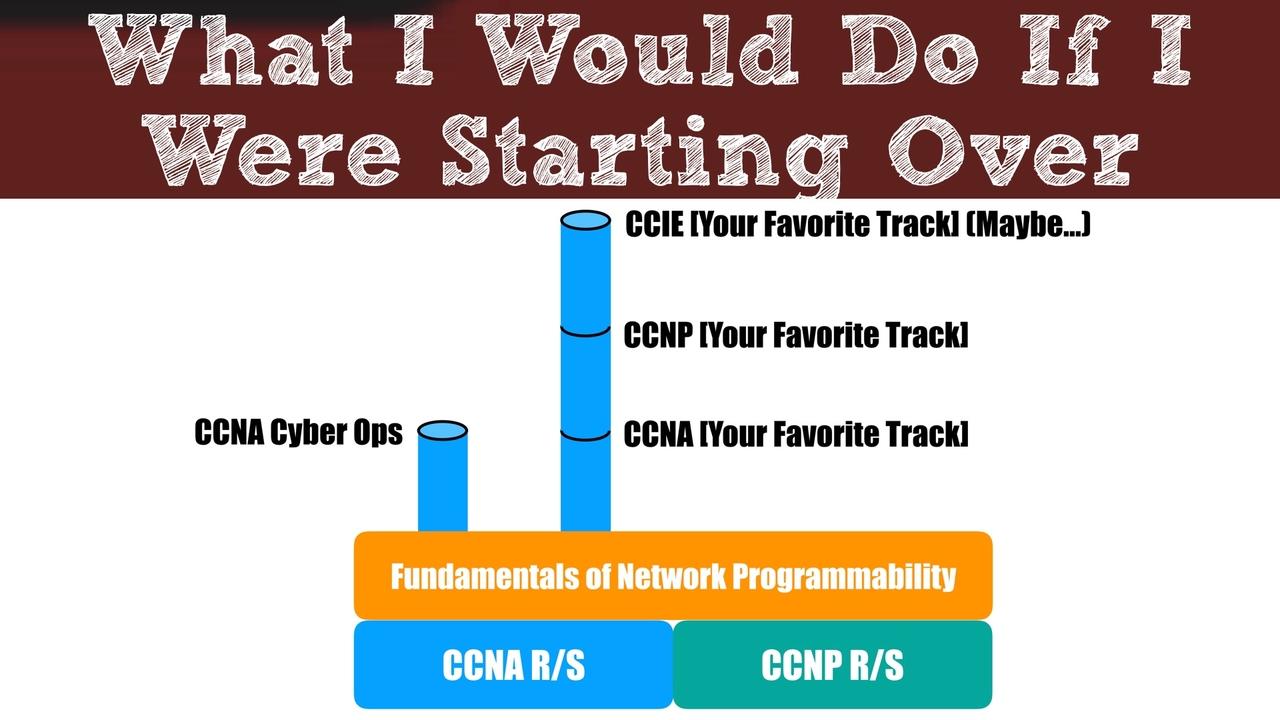
A common question I hear from people just getting into the Cisco world is, “Kevin, what would you do if you were starting from scratch?” Sometimes, that question takes the form of, “Which track (e.g. ...
The Auto Smartports feature available on Cisco Catalyst switches allows a port to automatically detect that you’ve attached a device it can recognize (e.g. a Cisco IP Phone, wireless access point, vid...
Some of my blog posts (most of them, in fact) focus on teaching you some technical content or offer career advice. But, sometimes, I just need to share a major milestone with you. That’s what I’m doin...
Software Defined Networking (SDN) can use a network controller to help orchestrate the monitoring and configuration of multiple network devices, allowing for faster configuration and more scalability....
Before Cisco had a Collaboration track, they had a Voice track. One of the courses in that track’s curriculum was the CVOICE course, and it really got into the configuration of H.323 gateways. I actua...
Many people ask me what technology (e.g. route/switch, collaboration, data center, etc.) they should pursue, based on industry demand. For years, my response has been, “There’s demand in all of those ...
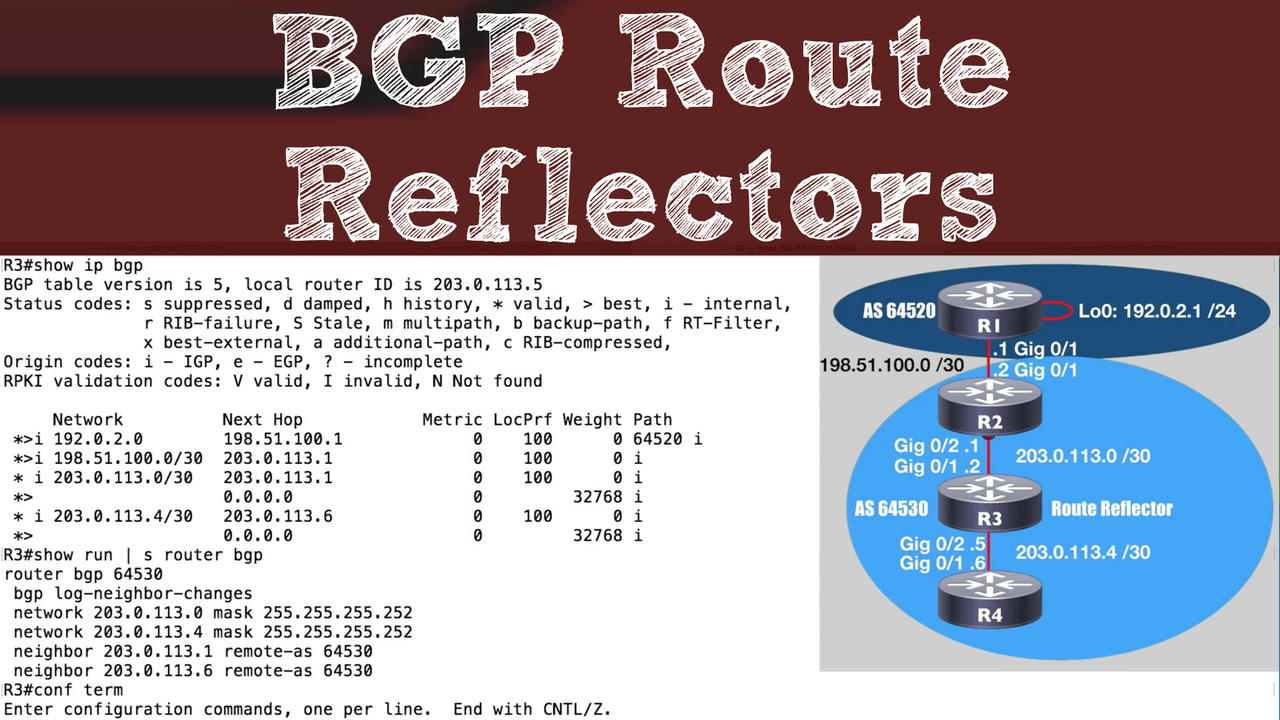
A BGP-speaking router, by default, will not advertise an Internal BGP (iBGP) route to an iBGP neighbor. One solution for this issue is to create a full mesh of neighborships within an Autonomous Syste...
We’ve all heard the saying, “Hindsight is 20/20.” However, a lack of clairvoyance about the future shouldn’t prevent us from boldly taking our next career step.
Steve Jobs told us, “You can't connect...
In June of 2017, I had the honor of presenting at CiscoLive for the first time. It was a great experience, and I thought you might enjoy checking it out. The session is on a Collaboration topic and is...
Cisco recently introduced their Catalyst 9000 Series switches. One unique feature of these switches is their ability to support containers. This podcast episode explains the concept of containers and ...
Malware poses an increasing threat to network devices. Recently, malware has been used to install ransomware on computers, which encrypts data on the computers' hard drives and demands money for the d...
Recently, I bought the book Deep Work, by Cal Newport. The book gives us a strategy for becoming much more productive. In hopes that you’ll read the book too and really apply it in your work, let me t...
You might be hearing the term Cisco Spark used a lot these days. But what exactly is it?
That's what you'll learn in this video. Enjoy!
Kevin Wallace, CCIEx2 (R/S and Collaboration) #7945
Back in my high school days, I took a class in mythology, and one of the stories that really stands out to me is the story of the Sirens. These Sirens were alluring creatures, with amazing voices, and...
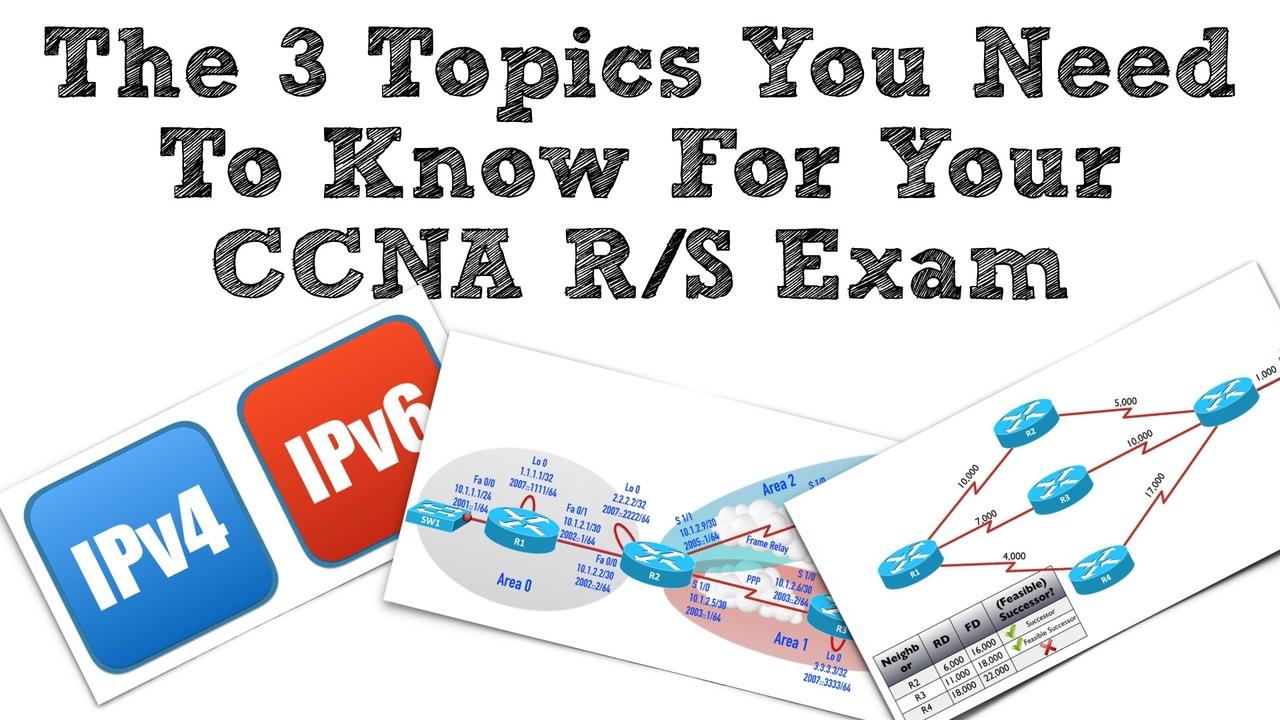
Studying for your CCNA R/S (200-125) exam? If so, a perusal of the exam topics list can be daunting. Clearly, you’re going to spend a significant amount of time getting at least a passing familiarity ...
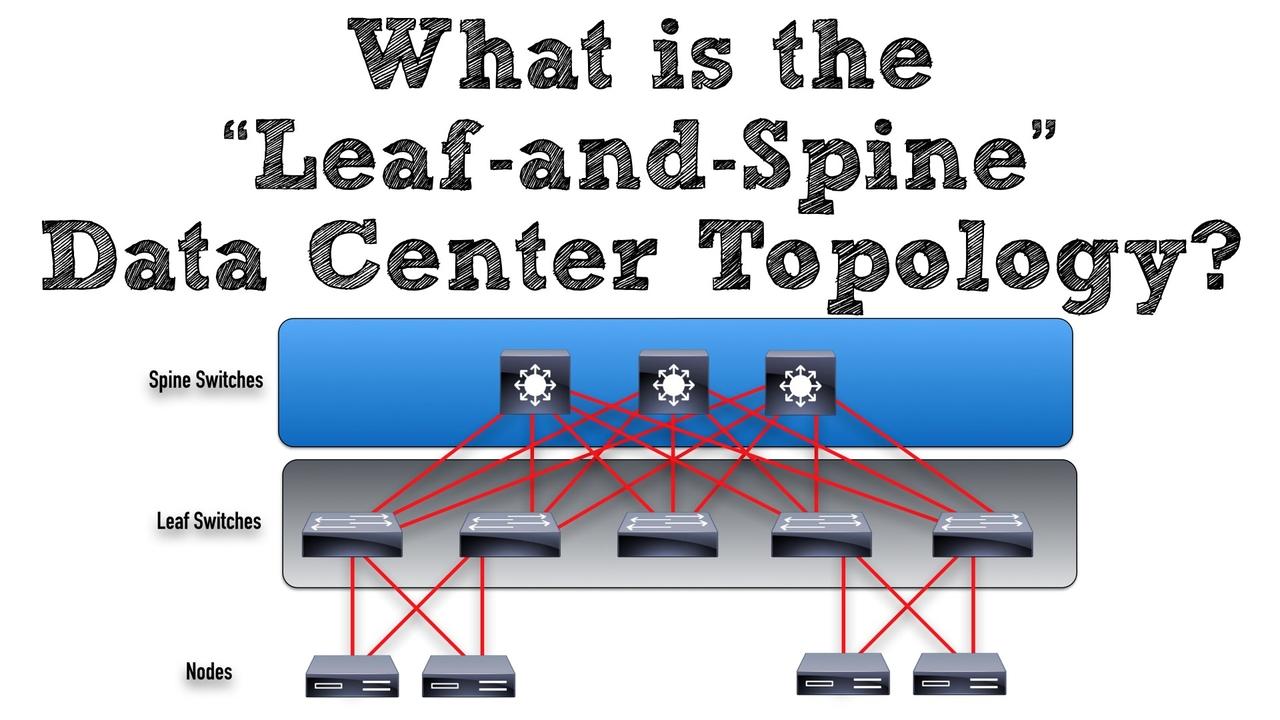
For decades, we’ve heard about Cisco’s three-tier network design where we had the following layers: (1) Access, (2) Distribution, and (3) Core. The Access Layer connected to our end devices (e.g. clie...
Are you going to Cisco Live US (CLUS) 2017 in Las Vegas? If so, you might want to come check out my session. It's entitled Number Globalization and Localization for CCIE Collaboration Candidates. But,...
It was 1989 when I first laid hands on a Cisco router. Specifically, it was a Cisco AGS+ router. Well, actually, it was called a “brouter,” because it did both bridging (software-based Layer 2 switchi...
The day-to-day tasks of Cisco network engineers are in the midst of a major industry shift. Specifically, we’re moving away from traditional command line interface (CLI) commands, and moving towards h...
This blog post wraps up our series on Understanding EIGRP by discussing two final topics:
- The EIGRP Router ID
- EIGRP's Neighborship Requirements
Let's begin our discussion by considering the EIG...
Typically, an EIGRP-speaking router dynamically discovers its neighbors, by sending multicast Hello messages. However, there is an option to statically configure those neighbors, and communicate with ...