THE BLOG
We’ve all heard the saying, “Hindsight is 20/20.” However, a lack of clairvoyance about the future shouldn’t prevent us from boldly taking our next career step.
Steve Jobs told us, “You can't connect...
In this post, I'm excited to share with you my latest podcast episode, where I'm interviewing my good friend and world-renowned Cisco trainer Anthony Sequeira.
In this episode, Anthony discusses:
-
...
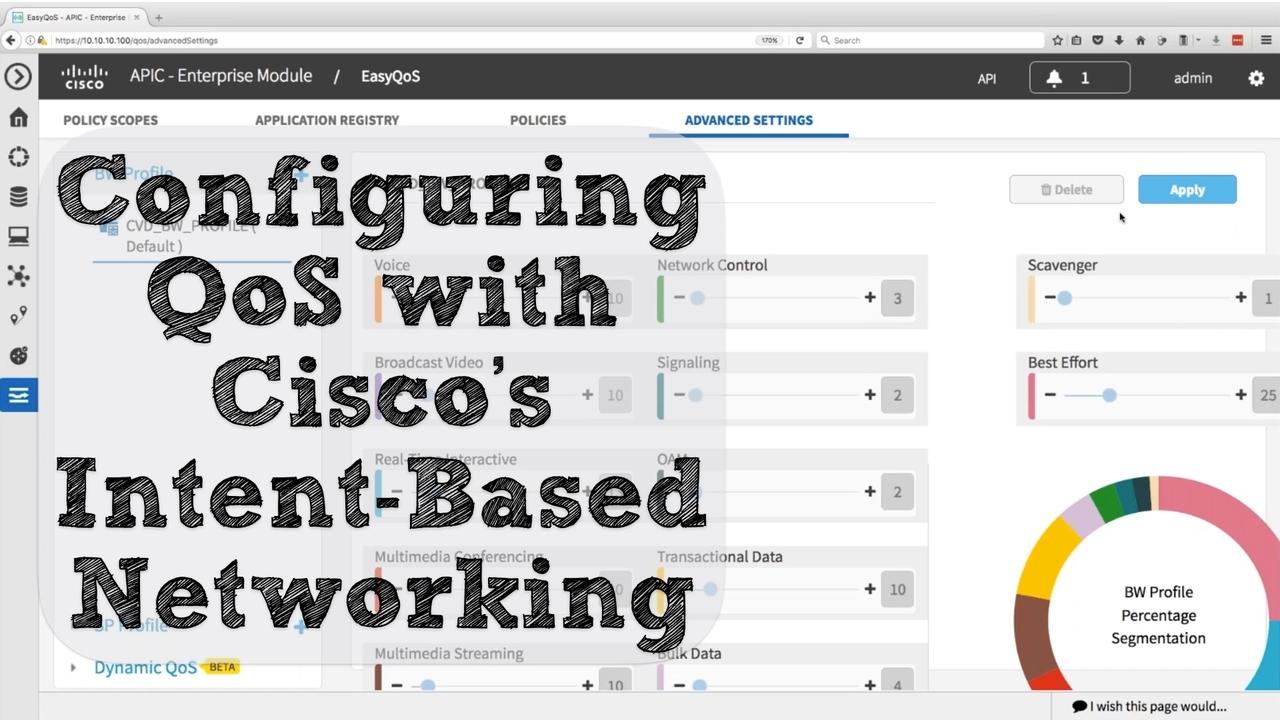
Over the past few months, you might have noticed Cisco’s publicity push regarding intent-based networking. The first time I saw this new brand messaging was at the Las Vegas McCarran Internation...
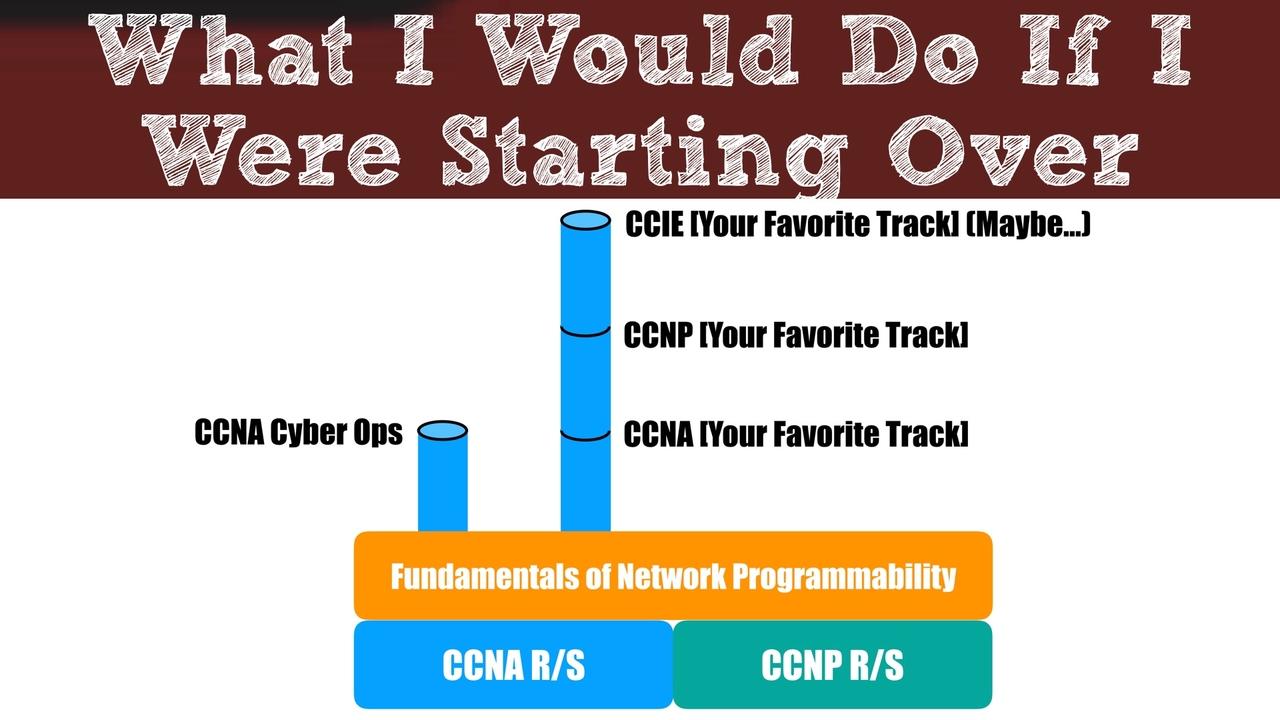
A common question I hear from people just getting into the Cisco world is, “Kevin, what would you do if you were starting from scratch?” Sometimes, that question takes the form of, “Which track (e.g. ...
Software Defined Networking (SDN) can use a network controller to help orchestrate the monitoring and configuration of multiple network devices, allowing for faster configuration and more scalability....
Many people ask me what technology (e.g. route/switch, collaboration, data center, etc.) they should pursue, based on industry demand. For years, my response has been, “There’s demand in all of those ...
We’ve all heard the saying, “Hindsight is 20/20.” However, a lack of clairvoyance about the future shouldn’t prevent us from boldly taking our next career step.
Steve Jobs told us, “You can't connect...
Recently, I bought the book Deep Work, by Cal Newport. The book gives us a strategy for becoming much more productive. In hopes that you’ll read the book too and really apply it in your work, let me t...
Back in my high school days, I took a class in mythology, and one of the stories that really stands out to me is the story of the Sirens. These Sirens were alluring creatures, with amazing voices, and...
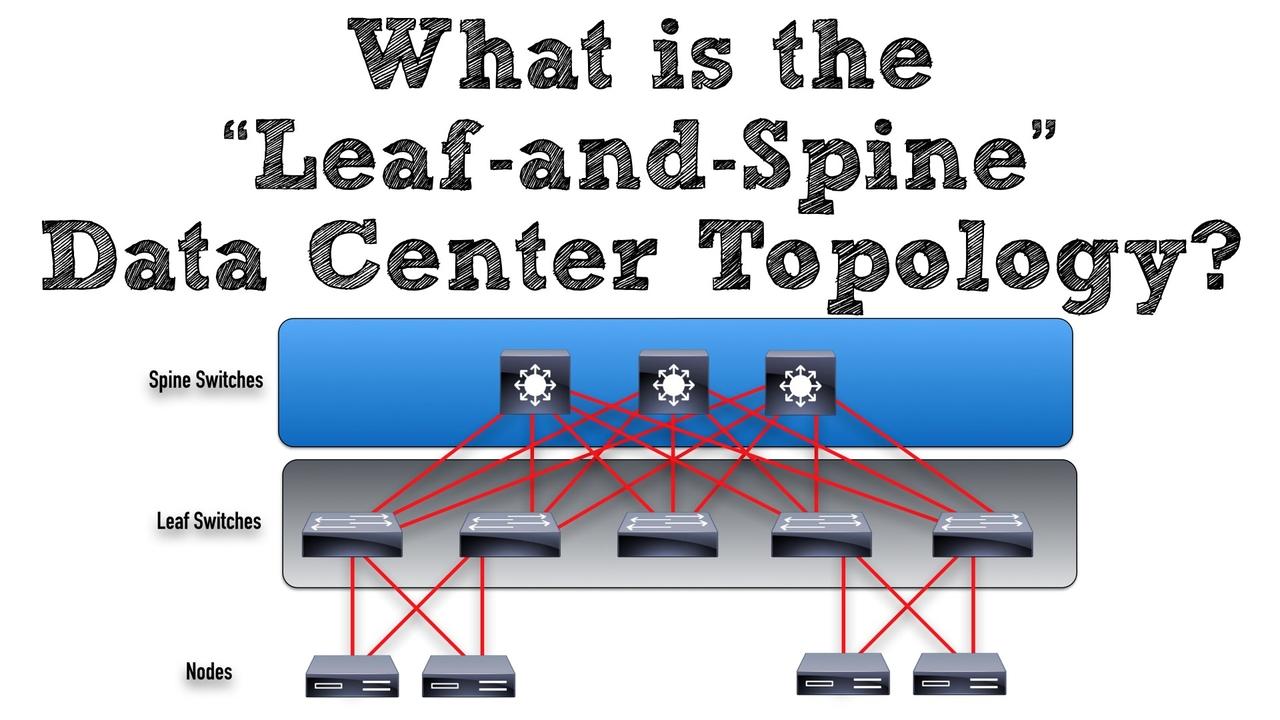
For decades, we’ve heard about Cisco’s three-tier network design where we had the following layers: (1) Access, (2) Distribution, and (3) Core. The Access Layer connected to our end devices (e.g. clie...
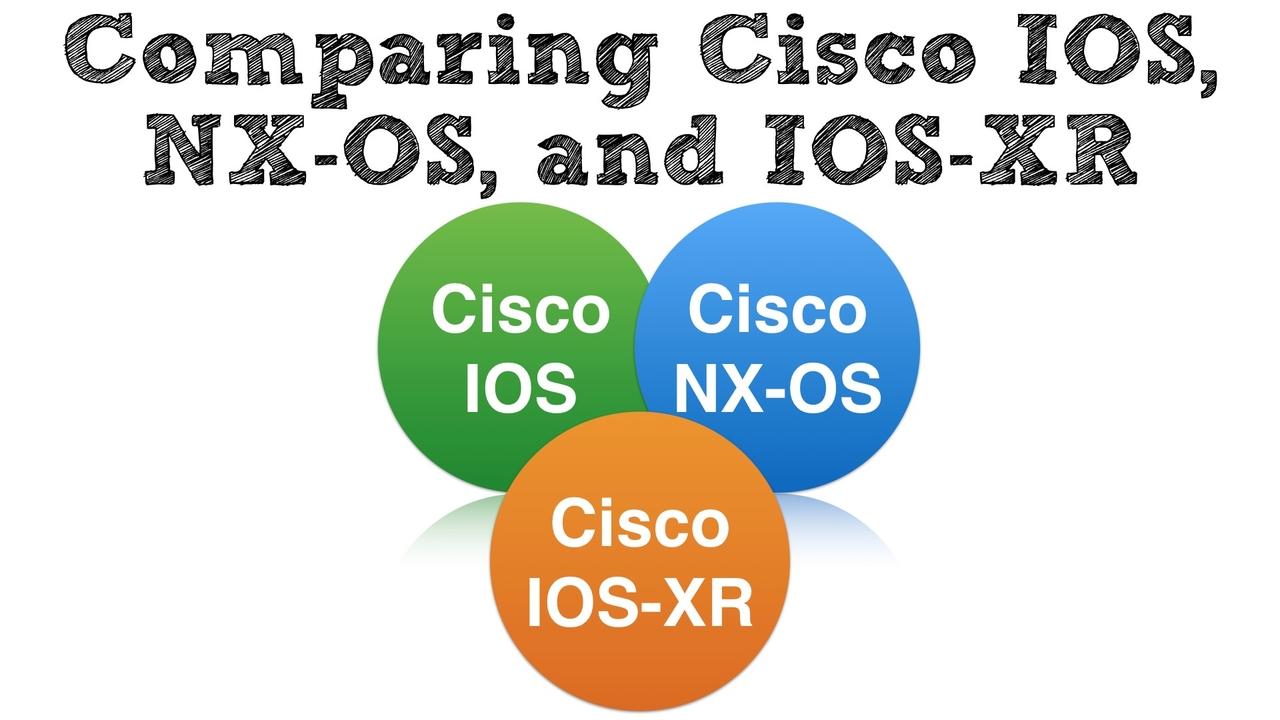
It was 1989 when I first laid hands on a Cisco router. Specifically, it was a Cisco AGS+ router. Well, actually, it was called a “brouter,” because it did both bridging (software-based Layer 2 switchi...
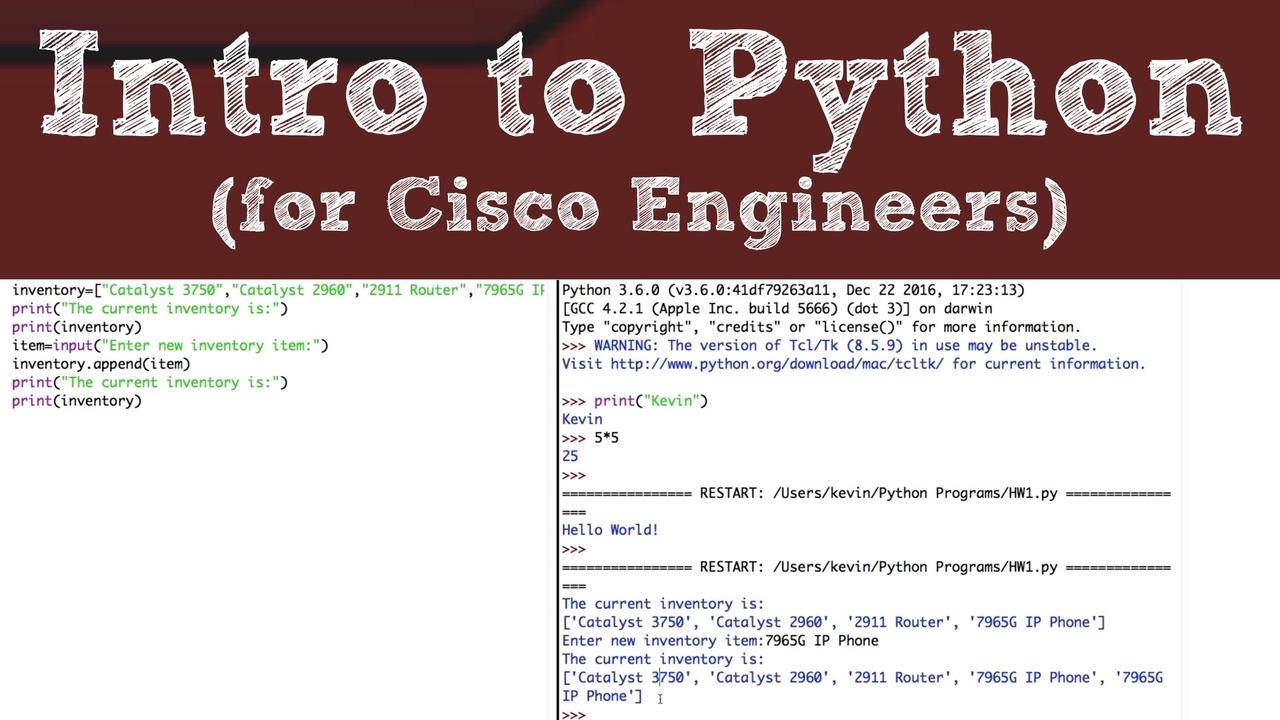
The day-to-day tasks of Cisco network engineers are in the midst of a major industry shift. Specifically, we’re moving away from traditional command line interface (CLI) commands, and moving towards h...
It's another one of those buzzwords we're hearing a ton these days, the Internet of Things, or IoT for short.
But what exactly is it, and how's it going to impact us as networking professionals? That...

You’ve earned your certifications. Maybe you have a college degree, and hopefully some technical experience. Now, it’s time to sell yourself to a prospective employer. We all know first impressions ...

There are lots of things that I intend to get around to, sooner or later. One day, I’m going to clean out a bunch of old clothes from my closet. One day, I’m going to clean out my garage, and get it...

It’s a timeless paradox… “How can I get a job without experience, and how can I get experience without a job?” If you find yourself in such a situation, this blog post is going to show you a couple ...
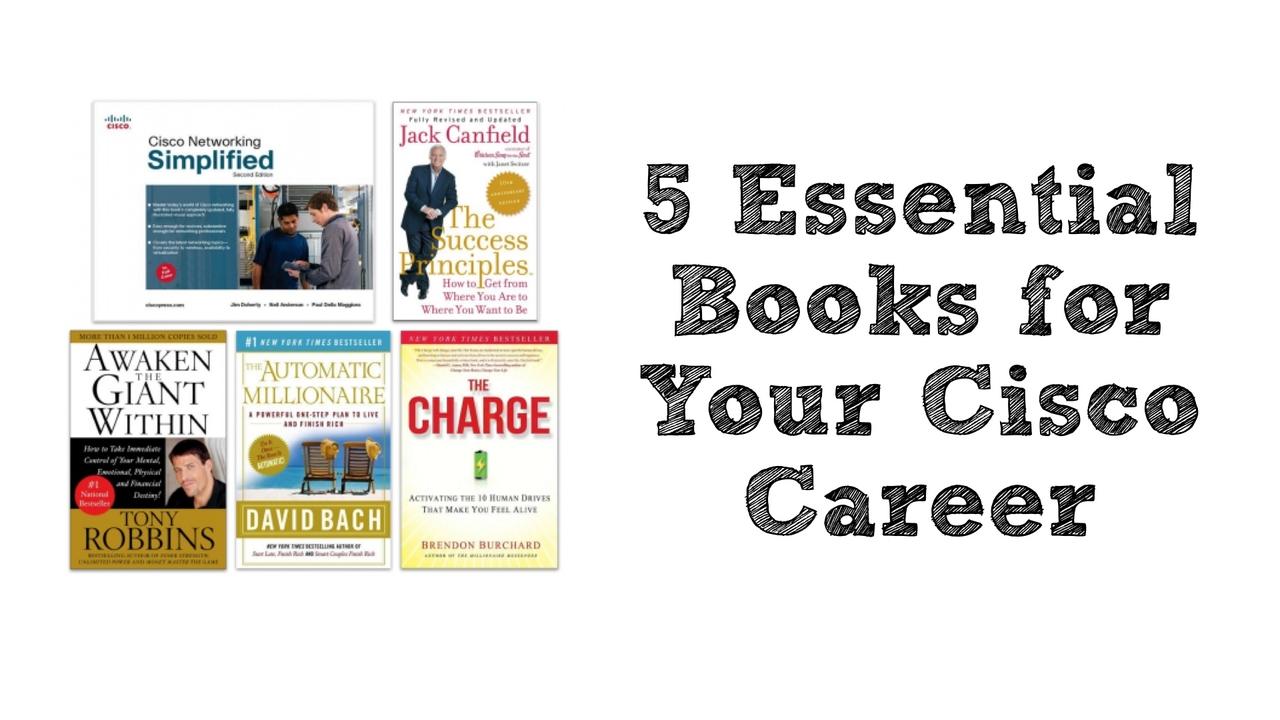
When I was around 20 years old, I used to go into bookstores and look for a book (something on a technical topic, a business biography, or on personal development) that I could afford. However, I rece...

Having the appropriate Cisco initials after your name (e.g. CCNA, CCNP, or CCIE) is a shortcut way of letting someone know your relative skill level. Even if you’ve got the skills and are at the top...

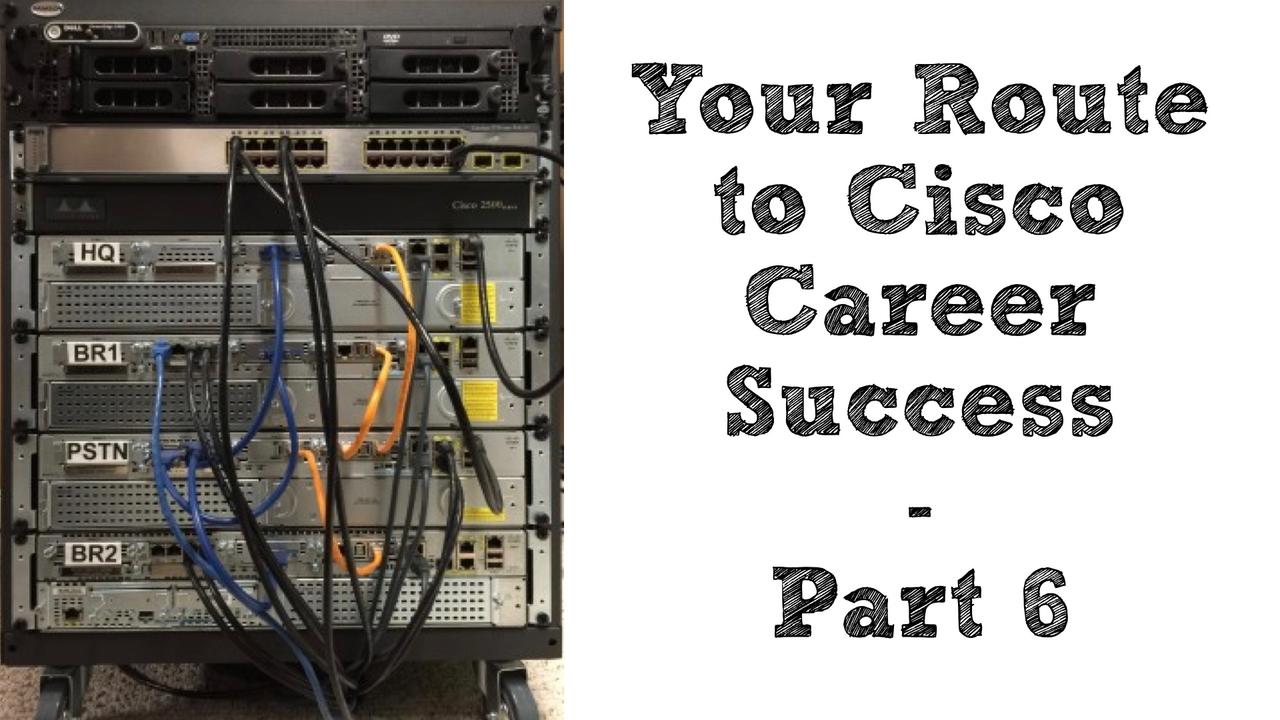
While documentation is indispensable in your mastery of Cisco technologies, at some point you have to “get your hands dirty.” In other words, you have to actually configure the routers, switches, an...

In high school, I really, really disliked reading. My reading speed was slow, and I found most of the assigned books were boring to me. Since this was back in the 1980s, before audio books really to...

While having lofty goals is key to propelling your career into the stratosphere, if you don’t have time to take action on your goals, what good are they? I shouldn’t say that you don’t have time. Af...
The way you start your day can have a huge impact on your productivity. Over the past few months, I’ve been experimenting with creating a “morning ritual,” which is a collection of energizing and moti...
Walt Disney is one of my personal heroes, and the following quote from him beautifully sets the stage for this blog post’s topic, curiosity:
We keep moving forward, opening new doors, and doing new t...
In a previous blog post we considered how to effectively set our goals to reach our “destination address.” However, no matter how well we plan, it seems that occasionally, life gets in the way. That’s...
When you see an advertisement for Disney Parks, and they show their tag line, The Place Where Dreams Come True, you might conjure up images of children meeting their favorite pirate or princess (by th...
About three years ago, I wrote a little e-book entitled Your Route to Cisco Career Success. Although it’s available in Kindle format from Amazon, you can download a free PDF of the bookHERE. Since the...
John Chambers has been the CEO of Cisco since January of 1995, but on July 26, 2015 he is stepping down and going into semi-retirement. Replacing him at the helm of Cisco is Chuck Robbins.
To honor J...

Just a few days ago, I returned from Cisco Live 2015, which was held in San Diego, California. As always, is was an educational, exhausting, and exciting week.
Enjoying Cisco Live 2015 With My Wife...
 In the first three parts of the Lessons I Learned from Disney series, we’ve talked about lessons learned when I was working at Walt Disney World. However, in this installment, let’s discuss a lesson l...
In the first three parts of the Lessons I Learned from Disney series, we’ve talked about lessons learned when I was working at Walt Disney World. However, in this installment, let’s discuss a lesson l...
 At some point in your networking career, you are almost certainly going to face the dreaded technical interview. In this blog posting, let’s answer the question, “How do you go in and come across as t...
At some point in your networking career, you are almost certainly going to face the dreaded technical interview. In this blog posting, let’s answer the question, “How do you go in and come across as t...
 Mid afternoon, around 3:00 pm, is a prime time for checking into hotels, and the same holds true for Disney’s many resorts. These days, when you check into a Disney resort, you’re given a Magic Band, ...
Mid afternoon, around 3:00 pm, is a prime time for checking into hotels, and the same holds true for Disney’s many resorts. These days, when you check into a Disney resort, you’re given a Magic Band, ...

Back in 2000, when I was working at Disney World as a Network Design Specialist, all disney.com e-mail accounts ran on two e-mail servers affectionately known and Pain and Panic (named after the sha...
 Anyone that knows my family and me, knows that we are huge fans of all things Disney. Besides just being a guest at various Disney destinations, I was privileged to be a cast member for the Walt Disne...
Anyone that knows my family and me, knows that we are huge fans of all things Disney. Besides just being a guest at various Disney destinations, I was privileged to be a cast member for the Walt Disne...
For years, the debate has raged about which is better. Is it better to focus on getting certifications or to earn a college-degree? Excellent points are to be made on each side of the argument. This i...

You’ve got a massive Cisco Press library; you’ve bookmarked key websites; and you’ve even subscribed to my blog :) Hopefully, you are super disciplined, and you’ve carved out dedicated chunks of tim...