THE BLOG
 Afew weeks ago, I made a blog post for those of you working towards your CCIE Collaboration certification. It covered how to configure a Cisco Unified Communications Manager Express (CUCME) router to ...
Afew weeks ago, I made a blog post for those of you working towards your CCIE Collaboration certification. It covered how to configure a Cisco Unified Communications Manager Express (CUCME) router to ...
 For years, my main Cisco focus was voice. I taught the the CCNA Voice and CCNP Voice courses for over a decade and earned my Voice CCIE in 2012, and then migrated that to a Collaboration CCIE in 2014....
For years, my main Cisco focus was voice. I taught the the CCNA Voice and CCNP Voice courses for over a decade and earned my Voice CCIE in 2012, and then migrated that to a Collaboration CCIE in 2014....
John Chambers has been the CEO of Cisco since January of 1995, but on July 26, 2015 he is stepping down and going into semi-retirement. Replacing him at the helm of Cisco is Chuck Robbins.
To honor J...

Just a few days ago, I returned from Cisco Live 2015, which was held in San Diego, California. As always, is was an educational, exhausting, and exciting week.
Enjoying Cisco Live 2015 With My Wife...
Did you know you can make a wireless router act as a wireless access point to extend the range of your network?
This video shows you how.
This video is a sample from my new CompTIA Network+ (N10-0...
The new CompTIA Network+ exam (N10-006) is out, and one of the little-known exam topics is SCADA.
Find out what it’s all about in this video.
This video is a sample from my new CompTIA Network+ (N...
 In the first three parts of the Lessons I Learned from Disney series, we’ve talked about lessons learned when I was working at Walt Disney World. However, in this installment, let’s discuss a lesson l...
In the first three parts of the Lessons I Learned from Disney series, we’ve talked about lessons learned when I was working at Walt Disney World. However, in this installment, let’s discuss a lesson l...
This video identifies the need for Quality of Service (QoS) and gets you acquainted with several QoS tools.
This video is a sample from my new CompTIA Network+ (N10-006) Complete Video Course, and ...
 At some point in your networking career, you are almost certainly going to face the dreaded technical interview. In this blog posting, let’s answer the question, “How do you go in and come across as t...
At some point in your networking career, you are almost certainly going to face the dreaded technical interview. In this blog posting, let’s answer the question, “How do you go in and come across as t...
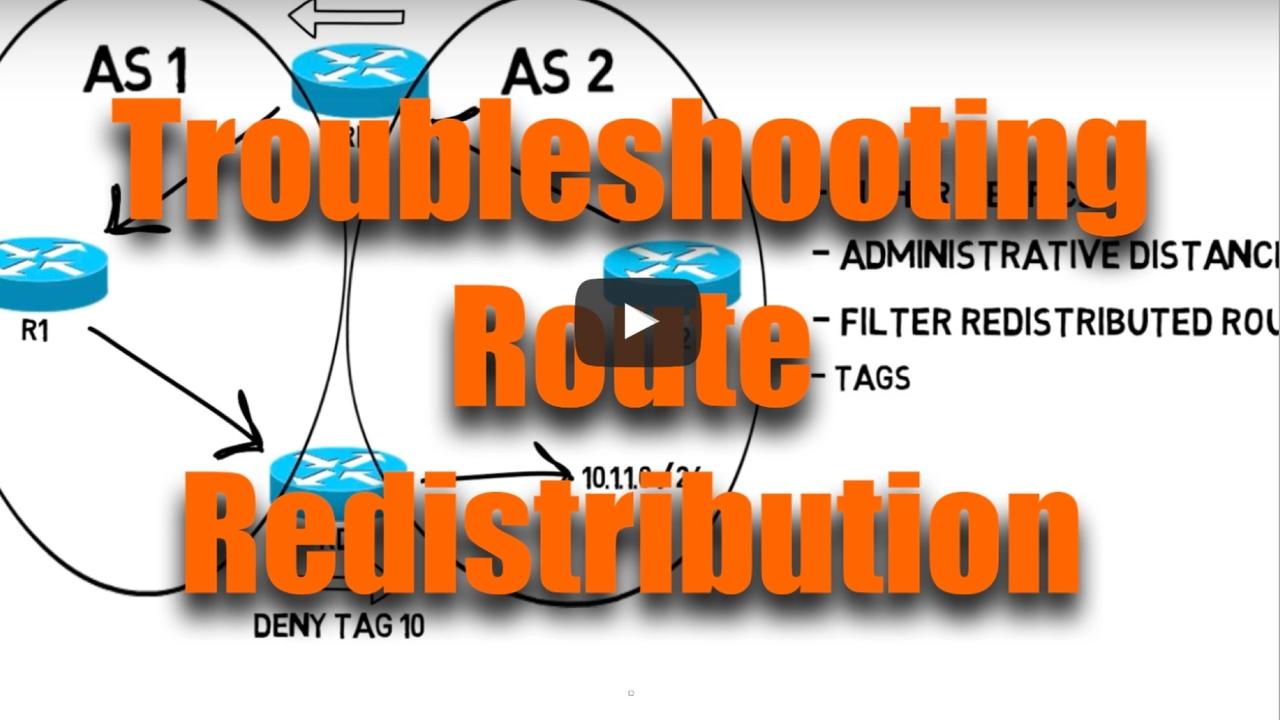
This video shows you how to troubleshoot a route redistribution scenario with multiple redistribution points.
This video is a sample from my new CCNP R/S v2 Complete Video Course Library (which inc...
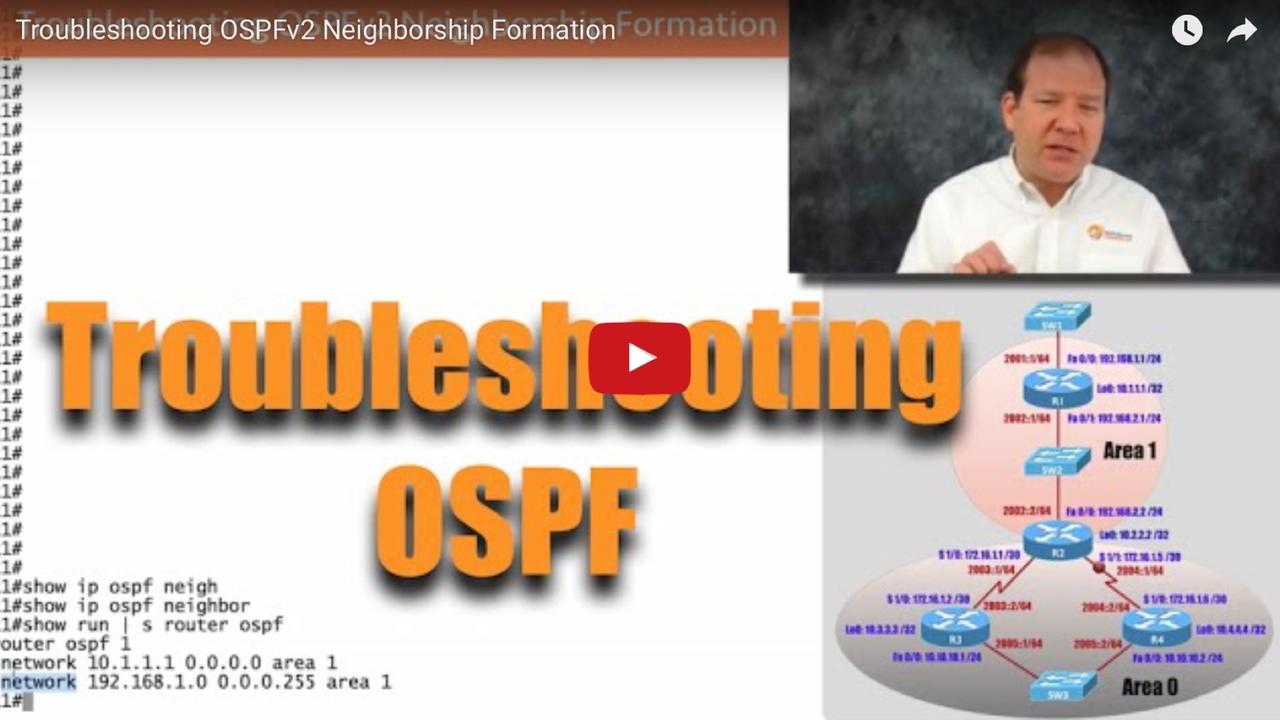
In this new video, you’ll learn common issues that can prevent an OSPFv2 neighborship from forming. Then, you’ll walk through a sample OSPF troubleshooting scenario.
This video is a sample from ...
 Mid afternoon, around 3:00 pm, is a prime time for checking into hotels, and the same holds true for Disney’s many resorts. These days, when you check into a Disney resort, you’re given a Magic Band, ...
Mid afternoon, around 3:00 pm, is a prime time for checking into hotels, and the same holds true for Disney’s many resorts. These days, when you check into a Disney resort, you’re given a Magic Band, ...

Back in 2000, when I was working at Disney World as a Network Design Specialist, all disney.com e-mail accounts ran on two e-mail servers affectionately known and Pain and Panic (named after the sha...
 Anyone that knows my family and me, knows that we are huge fans of all things Disney. Besides just being a guest at various Disney destinations, I was privileged to be a cast member for the Walt Disne...
Anyone that knows my family and me, knows that we are huge fans of all things Disney. Besides just being a guest at various Disney destinations, I was privileged to be a cast member for the Walt Disne...
Happy New Year!
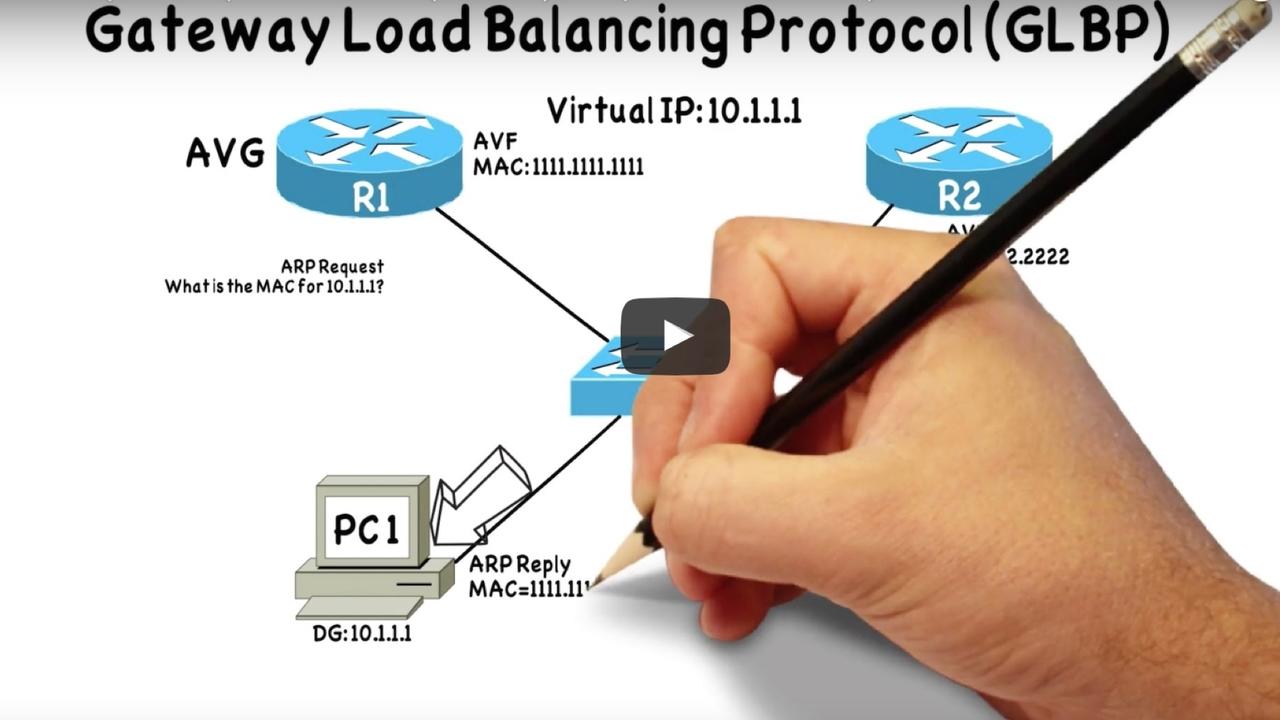
If one of your goals for 2015 is to earn your CCNP R/S certification, you might want to check out a new video I did.
The video discusses the theory of GLBP, a First Hop Redundancy Pr...
For years, the debate has raged about which is better. Is it better to focus on getting certifications or to earn a college-degree? Excellent points are to be made on each side of the argument. This i...

You’ve got a massive Cisco Press library; you’ve bookmarked key websites; and you’ve even subscribed to my blog :) Hopefully, you are super disciplined, and you’ve carved out dedicated chunks of tim...
This video from my ROUTE Complete Video Course demonstrates how BGP Peer Groups can help conserve a router’s CPU resources if the router is doing BGP route filtering with multiple BGP neighbors.